What Is the MITRE ATT&CK Framework?
MITRE ATT&CK® stands for MITRE Adversarial Tactics, Techniques, and Common Knowledge (ATT&CK). The MITRE ATT&CK framework is a curated knowledge base and model for cyber adversary behavior, reflecting the various phases of an adversary's attack lifecycle and the platforms they are known to target. The tactics and techniques abstraction in the model provide a common taxonomy of individual adversary actions understood by both offensive and defensive sides of cybersecurity. It also provides an appropriate level of categorization for adversary action and specific ways of defending against it.
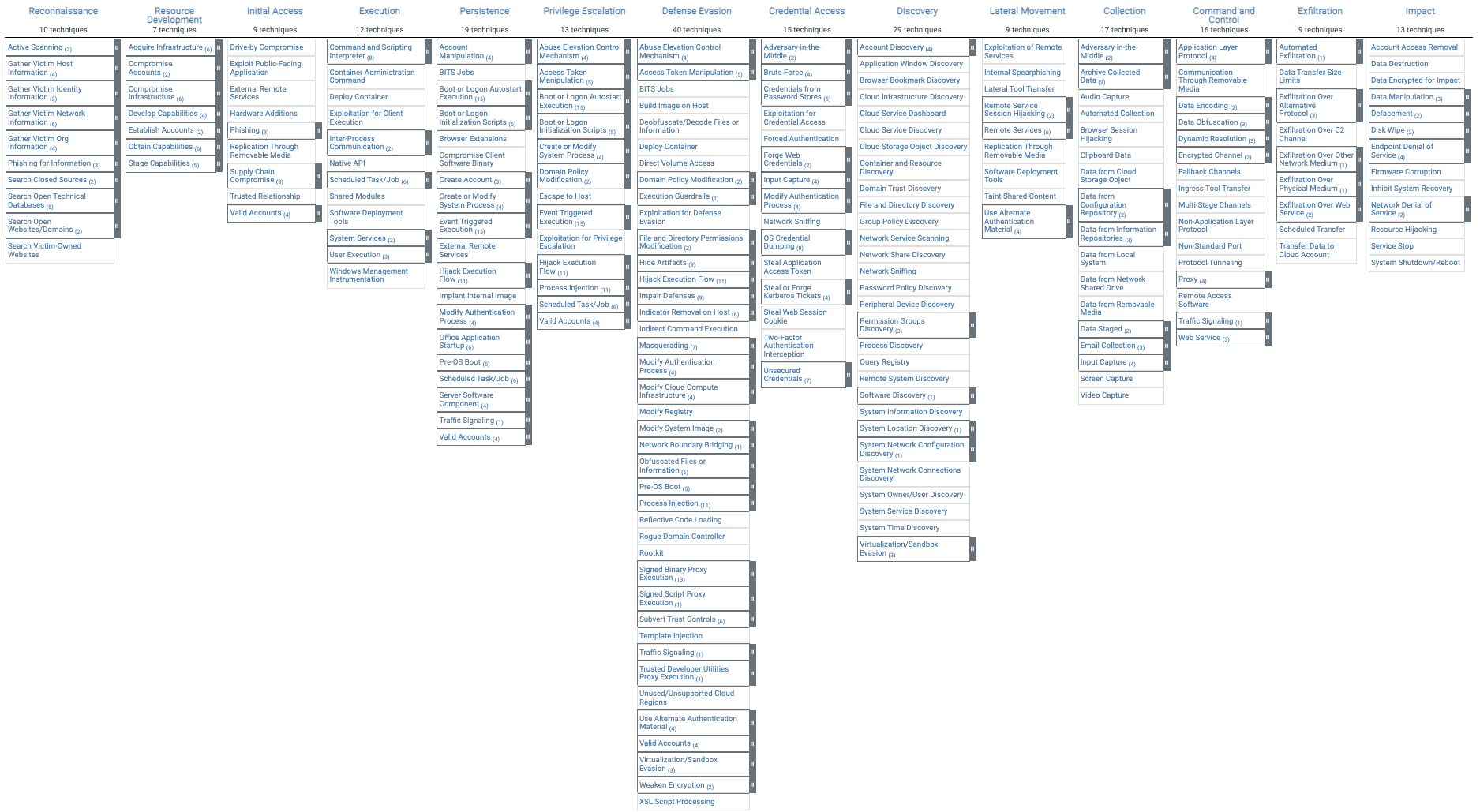
The behavioral model presented by ATT&CK contains the following core components:
- Tactics denoting short-term, tactical adversary goals during an attack (the columns);
- Techniques describing the means by which adversaries achieve tactical goals (the individual cells); and
- Documented adversary usage of techniques and other metadata (linked to techniques). [1]
MITRE ATT&CK was created in 2013 as a result of MITRE's Fort Meade Experiment (FMX) where researchers emulated both adversary and defender behavior in an effort to improve post-compromise detection of threats through telemetry sensing and behavioral analysis. The key question for the researchers was "How well are we doing at detecting documented adversary behavior?" To answer that question, the researchers developed ATT&CK, which was used as a tool to categorize adversary behavior.
MITRE ATT&CK now has three iterations:
ATT&CK for Enterprise
ATT&CK for Mobile
ATT&CK for ICS
Focuses on adversarial behavior in Windows, Mac, Linux, and Cloud environments.
Focuses on adversarial behavior on iOS and Android operating systems.
Focuses on describing the actions an adversary may take while operating within an ICS network.
MITRE ATT&CK is used worldwide across multiple disciplines including intrusion detection, threat hunting, security engineering, threat intelligence, red teaming, and risk management. [2]
What is in the MITRE ATT&CK Matrix?
The MITRE ATT&CK matrix contains a set of techniques used by adversaries to accomplish a specific objective. Those objectives are categorized as tactics in the ATT&CK Matrix. The objectives are presented linearly from the point of reconnaissance to the final goal of exfiltration or "impact". Looking at the broadest version of ATT&CK for Enterprise, which includes Windows, macOS, Linux, PRE, Azure AD, Office 365, Google Workspace, SaaS, IaaS, Network, and Containers, the following adversary tactics are categorized:
- Reconnaissance: gathering information to plan future adversary operations, i.e., information about the target organization
- Resource Development: establishing resources to support operations, i.e., setting up command and control infrastructure
- Initial Access: trying to get into your network, i.e., spear phishing
- Execution: trying the run malicious code, i.e., running a remote access tool
- Persistence: trying to maintain their foothold, i.e., changing configurations
- Privilege Escalation: trying to gain higher-level permissions, i.e., leveraging a vulnerability to elevate access
- Defense Evasion: trying to avoid being detected, i.e., using trusted processes to hide malware
- Credential Access: stealing accounts names and passwords, i.e., keylogging
- Discovery: trying to figure out your environment, i.e., exploring what they can control
- Lateral Movement: moving through your environment, i.e., using legitimate credentials to pivot through multiple systems
- Collection: gathering data of interest to the adversary goal, i.e., accessing data in cloud storage
- Command and Control: communicating with compromised systems to control them, i.e., mimicking normal web traffic to communicate with a victim network
- Exfiltration: stealing data, i.e., transfer data to cloud account
- Impact: manipulate, interrupt, or destroy systems and data, i.e., encrypting data with ransomware
Within each tactic of the MITRE ATT&CK matrix there are adversary techniques, which describe the actual activity carried out by the adversary. Some techniques have sub-techniques that explain how an adversary carries out a specific technique in greater detail. The full ATT&CK Matrix for Enterprise from the MITRE ATT&CK navigator is represented below:
MITRE ATT&CK for Enterprise, 2021
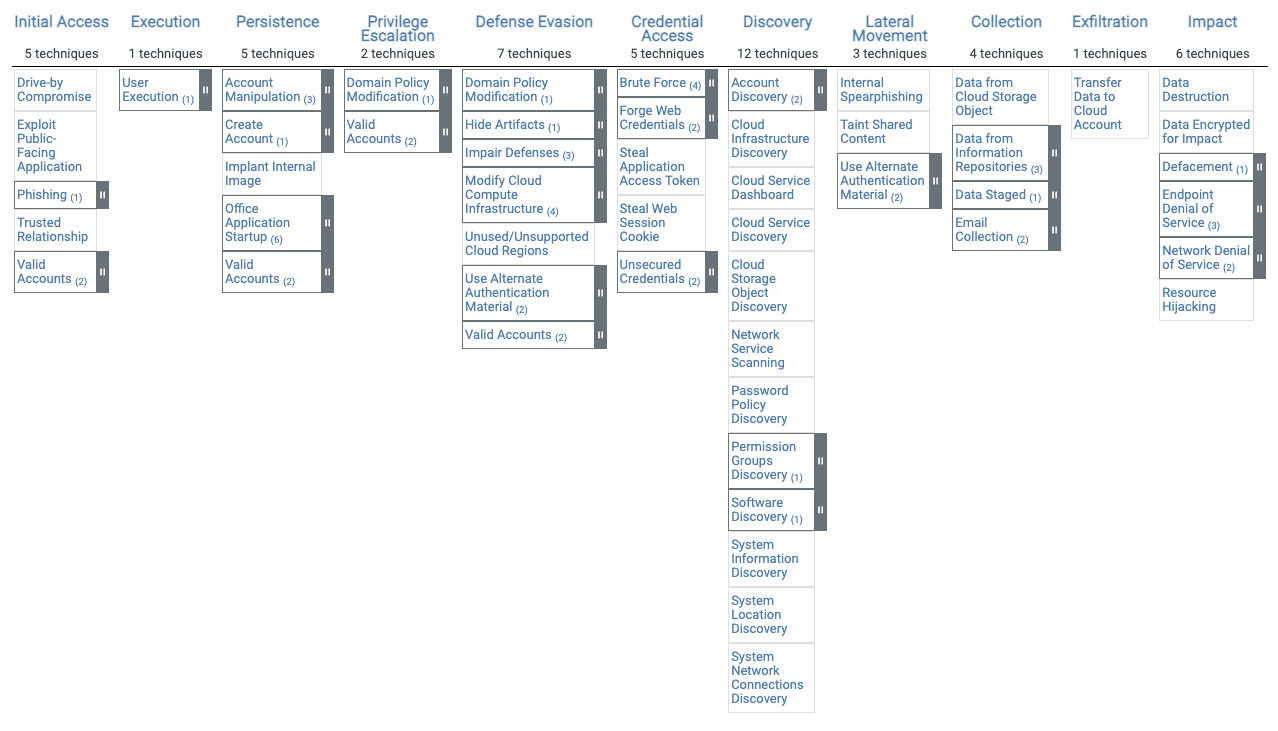
What is different about the MITRE ATT&CK for Cloud Matrix?
Within the MITRE ATT&CK for Enterprise matrix you will find a subsection, the MITRE ATT&CK for Cloud matrix, that contains a subset of the tactics and techniques from the broader ATT&CK Enterprise matrix. The MITRE ATT&CK Cloud matrix is different from the rest of the Enterprise Matrix because adversary behavior and the techniques used in a cloud attack do not follow the same playbook as attacks on Windows, macOS, Linux, or other enterprise environments.
MITRE ATT&CK techniques in Windows, macOS, Linux, and other related environments typically involve malware and entering a network that is owned and operated by the target organization.
MITRE ATT&CK techniques in AWS, Azure, Office 365, and other related environments do not typically involve malware, as the target environment is owned and operated by a third-party cloud service provider like Microsoft or Amazon. Without the ability to enter the victim's environment, the adversary will most often leverage native features of the CSP to enter the target victim's account, escalate privileges, move laterally, and exfiltrate data. An example of adversary behavior using the ATT&CK for Cloud framework is illustrated in the following example techniques:
Technique
Behavior
Initial Access
Uses stolen credentials to create a new account
Persistence
Adversary spear-phishes the victim, gaining credentials to AWS
Privilege Escalation
Uses valid account to change access permissions
Defense Evasion
Creates a new VM instance to bypass firewall rules
Credential Access
Steals access token to a database
Discovery
Locates target database
Lateral Movement
Uses application access token to access database
Collection
Mines information from the database
Exfiltration
Exfiltrates to adversary account in AWS
The entire ATT&CK for Cloud matrix can be seen below which shows its subset of the ATT&CK for Enterprise matrix tactics and techniques:
MITRE ATT&CK for Cloud, 2021
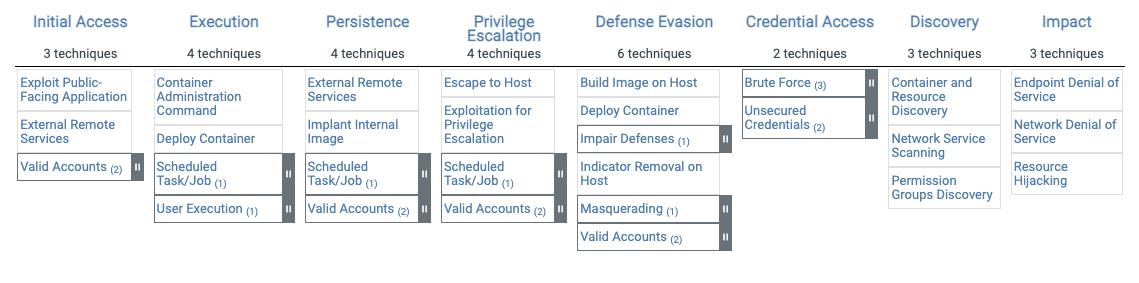
MITRE ATT&CK for Containers, 2021
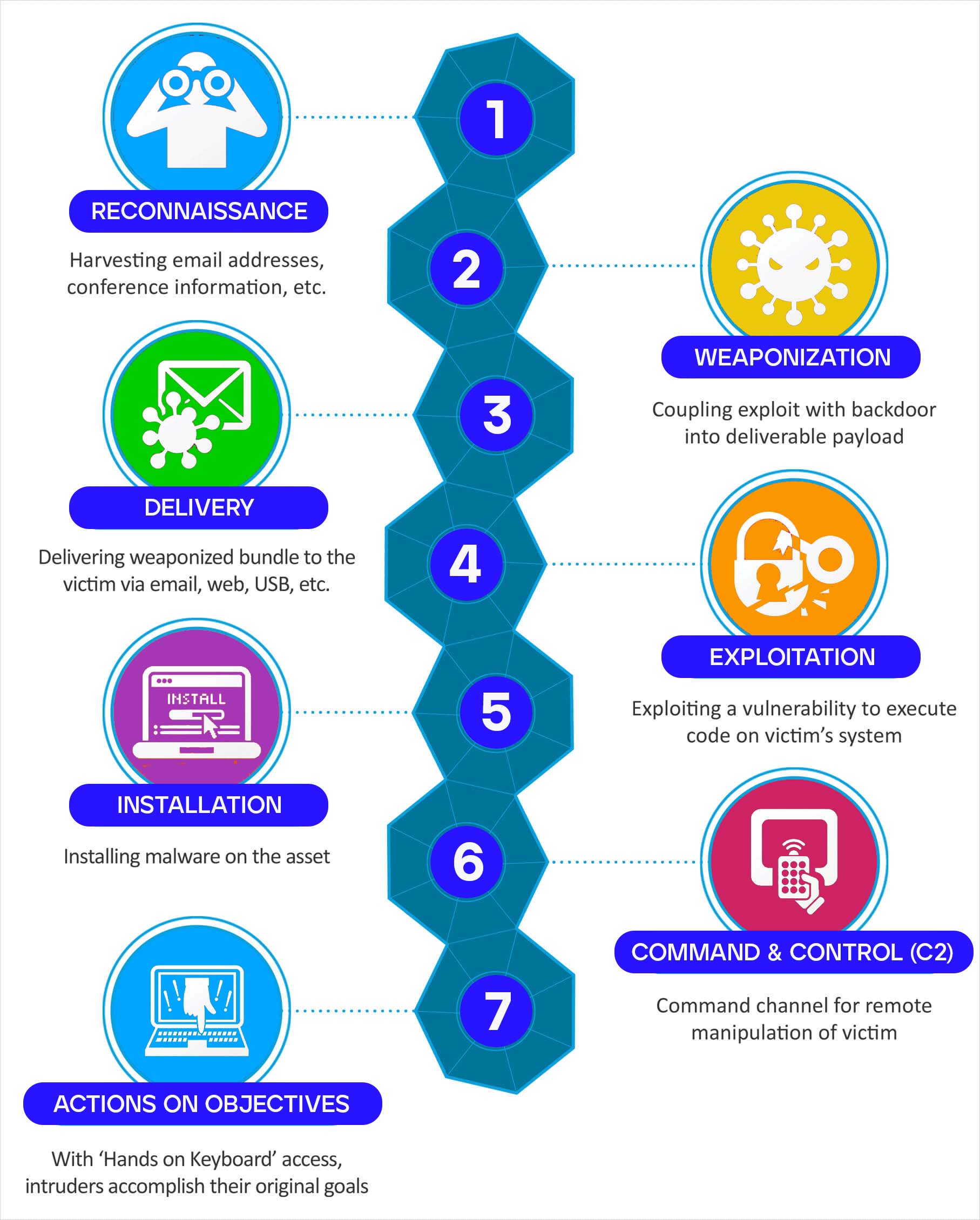
MITRE ATT&CK vs. the Cyber Kill Chain
The Lockheed Martin Cyber Kill Chain® is another well-known framework for understanding adversary behavior in a cyber-attack. The Kill Chain model contains the following stages, presented in sequence:
- Reconnaissance – Harvests email addresses, conference information, etc.
- Weaponization – Couples exploit with backdoor into deliverable payload.
- Delivery – Delivers weaponized bundle to the victim via email, web, USB, etc.
- Exploitation – Exploits a vulnerability to execute code on a victim's system.
- Installation – Installs malware on the asset.
- Command & Control (C2) – Includes command channel for remote manipulation.
- Actions on Objectives – Using 'Hands on Keyboards' access, intruders accomplish their original goals.
Lockheed Martin gives more detail on their Cyber Kill Chain framework in this graphic. [3]
There are two primary differences between MITRE ATT&CK and Cyber Kill Chain.
- First, the MITRE ATT&CK framework goes into significantly more depth on how each stage is conducted through ATT&CK techniques and sub-techniques. MITRE ATT&CK is regularly updated with industry input to keep up with the latest techniques so defenders update their own practices and attack modeling regularly.
- Second, the Cyber Kill Chain does not factor in the different tactics and techniques of a cloud-native attack, as discussed above. The Cyber Kill Chain framework assumes that an adversary will deliver a payload, such as malware, to the target environment; a method which is much less relevant in the cloud.
How Do You Use the MITRE ATT&CK Matrix?
The MITRE ATT&CK framework can help an organization in several ways. In general, the following are applicable benefits to adopting MITRE ATT&CK:
- Adversary Emulation: Assesses security by applying intelligence about an adversary and how they operate to emulate a threat. ATT&CK can be used to create adversary emulation scenarios to test and verify defenses.
- Red Teaming: Acts as an adversary to demonstrate the impact of a breach. ATT&CK can be used to create red team plans and organize operations.
- Behavioral Analytics Development: Links together suspicious activity to monitor adversary activity. ATT&CK can be used to simplify and organize patterns of suspicious activity deemed malicious.
- Defensive Gap Assessment: Determines what parts of the enterprise lack defenses and/or visibility. ATT&CK can be used to assess existing tools, or test new tools prior to purchasing, to determine security coverage and prioritize investment.
- SOC Maturity Assessment: Similar to Defensive Gap Assessment, ATT&CK can be used to determine how effective a security operations center (SOC) is at detecting, analyzing, and responding to breaches.
- Cyber Threat Intelligence Enrichment: Enhances information about threats and threat actors. ATT&CK allows defenders to assess whether they are able to defend against specific Advanced Persistent Threats (ATP) and common behaviors across multiple threat actors.
Implementing MITRE ATT&CK typically involves either manual mapping or integration with cybersecurity tools, the most common of which are Security Information and Event Management (SIEM), Endpoint Detection and Response (EDR), and Cloud Access Security Broker (CASB).
Using MITRE ATT&CK with a SIEM involves aggregating log data from endpoints, networks, and cloud services, identifying threats and mapping them to MITRE ATT&CK. Changes to security posture are then conducted in the security tools providing their log data, (i.e., EDR or CASB).
Using MITRE ATT&CK with EDR involves mapping events observed by the endpoint agent, allowing defenders to determine the phases of a threat event, assess associated risk, and prioritize response.
Resources
MITRE Evaluation
Resources
Trellix has participated in all MITRE ATT&CK evaluations